How to Remove Locky and AutoLocky Ransomware for Free
|
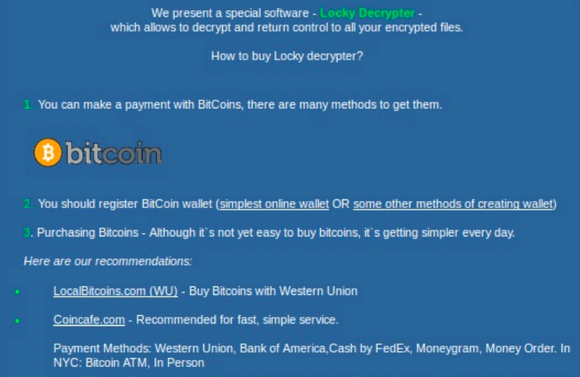
Ransomware is malicious software with the ability to encrypt files or rename files to deny user access. The purpose is to force computer users to pay a ransom, in order to obtain a private key or decryption program held by the cyber hijacker, which (hopefully) unlocks affected files and returns access to the user.
The Locky and AutoLocky ransomware, in this example, infect *Windows operating systems. Locky and AutoLocky ransomware are distributed via malicious .doc files, fake YouTube video links or disguised as an Adobe Flash Player update pop up notification. It is often sent as an email or messenger attachment. When a link or attachment is clicked, macros download and install the ransomware. Code is eventually rewritten with the hopes of circumventing future detection by bypassing firewalls and antimalware programs. * Note: If you open an infected Windows file in Linux, using Wine (shell program), it can also infect that O/S. Locky encrypts files with RSA-2048 and AES-1024 algorithm ciphers and randomly renames files, making them difficult or impossible to find. AutoLocky, not nearly as sophisticated as the original, adds an additional file extension (.locky) to the file name. That file extension, having no known program association, renders them unable to be opened. When a computer is infected with Locky, the user will get an instantaneous ransom notification. When a user of a computer infected with AutoLocky attempts to open an encrypted/locked file, they will get an Access Denied notification accompanied by instructions provided in an info.txt or info.html file on the desktop demanding payment payable in BitCoins. Both may or may not include a time limit to act before their "offer" is withdrawn. You will need Administrative Privileges, in order to accomplish this task.
1. Choose one of the free removal programs, linked to below, which are hosted on separate secure sites. 2. Download/Scan/Run in that order, for your own safety, as with any other file download. 3. Follow any instructions or prompts provided by the removal programs. 4. Reboot your computer, if necessary, to complete the removal operation. Hosted on https://www.pcrisk.com/
Hosted on https://decrypter.emsisoft.com/
Tips:
* Download/Scan/Open - in that order! * Always keep your antivirus/antimalware programs up to date, and use them! Warnings: * Even after paying a ransom, there is absolutely no guarantee that your files will ever be decrypted! Copyright 11/23/2016 All Rights Reserved. Questions? Comments? Contact Me |
|